PDF) RFID READER/WRITER FOR LF, HF, NFC, BLE · Smart MX3), MIFARE Ultralight, MIFARE Ultralight C, MIFARE Ultralight EV1, NTAG2xx, PayPass3), SLE44R35, SLE66Rxx (my-d move)3), Topaz - DOKUMEN.TIPS

hackerfantastic.crypto on Twitter: "The RSA passes use Mifare Ultralight-C type 2 tag with a basic lanyard, the RFID blocks read "BREAKMEIFYOUCAN!" with a 55 byte TEXT record for encoding attendee id &

MAGIC NTAG21X® / NTAG® I2C / MIFARE ULTRALIGHT® EV1 COMPATIBLE TAG - Access Control, KSEC, Magic Cards, Red Team Tools, RFID Access Cards, RFID NFC Tools - KSEC Solutions

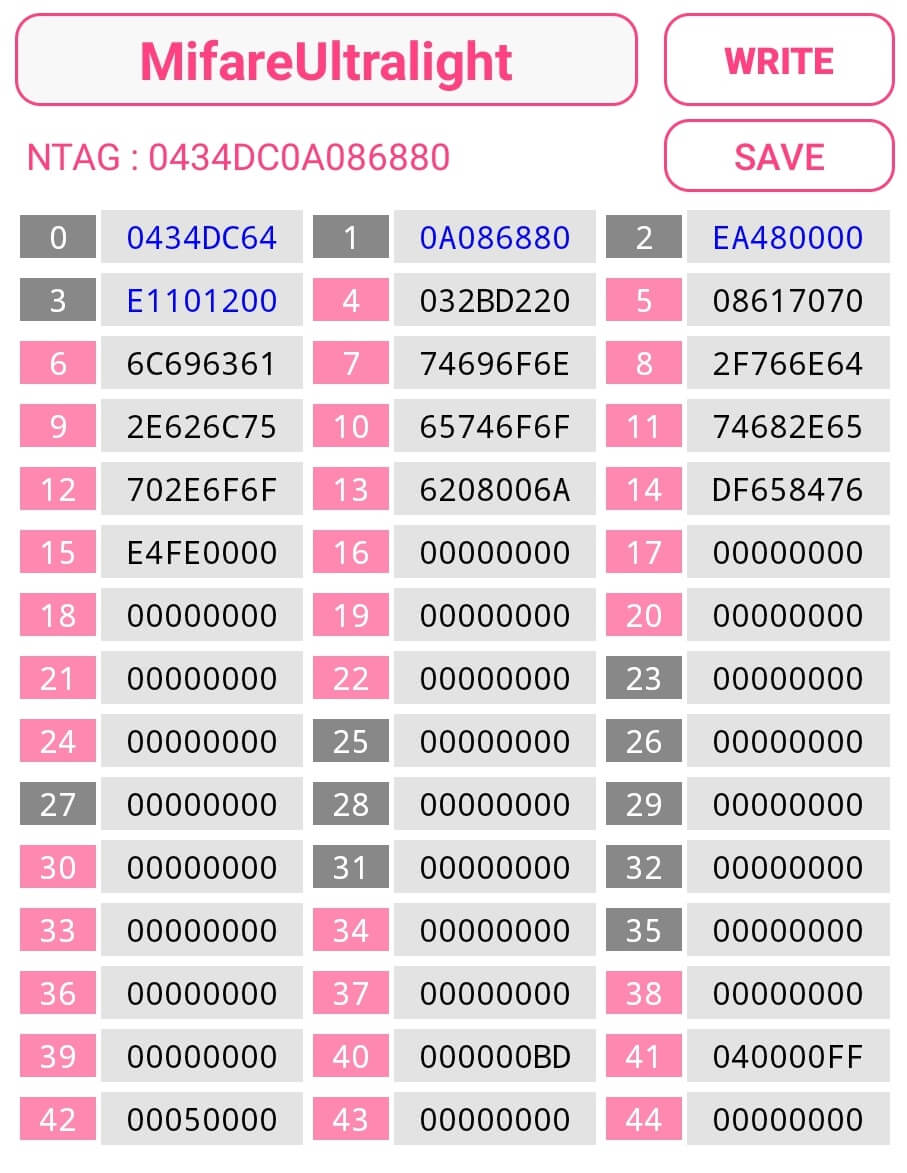





![Memory of a Mifare Ultralight tag[11] | Download Scientific Diagram Memory of a Mifare Ultralight tag[11] | Download Scientific Diagram](https://www.researchgate.net/publication/255593385/figure/fig6/AS:297841592422425@1448022377757/Memory-of-a-Mifare-Ultralight-tag11.png)